 The alarming rise of ransomware attacks is less shocking to those of us who’ve been in the industry for a long time. They grab the headlines, especially when they hit high-profile healthcare, education, and finance targets. But the reality is, there’s nothing new here. In fact, 76% of the vulnerabilities currently being exploited were first discovered between 2010 and 2019. Cybercriminals are leveraging these old weaknesses with the latest in AI and machine learning to maximize their impact.
The alarming rise of ransomware attacks is less shocking to those of us who’ve been in the industry for a long time. They grab the headlines, especially when they hit high-profile healthcare, education, and finance targets. But the reality is, there’s nothing new here. In fact, 76% of the vulnerabilities currently being exploited were first discovered between 2010 and 2019. Cybercriminals are leveraging these old weaknesses with the latest in AI and machine learning to maximize their impact.
This statistic comes from a new report on ransomware, which is worth going through to determine why old vulnerabilities are still a problem. Looking at this through the lens of “Is it a people problem?” could also shed some light on the future of ransomware attacks.
Ransomware Is on the Rise, and You’ll Never Be 100% Prepared
The increase in these attacks is something on the minds of most security leaders. When they happen, it’s cataclysmic and chaotic. It’s not just a breach — it’s the inability to access your data and disruption to your customers. There are monetary and reputational ramifications. The question is always, “Should you pay?”
It’s a polarizing question, with many adamant that not paying will convince other hackers not to attack them. That, of course, is flawed logic. I can tell you that cybercriminals don’t care what your position is. They are trying to maximize their return by infiltrating as many systems as possible. The answer changes when the stakes are higher, like exploiting vulnerabilities in medical devices.
This is rare, so the answer depends on your preparedness for such an attack. Do you have backups that are current? How fast can you restore systems? How advanced are your forensics?
If you’re not in a position to ensure business continuity, you can make strides to do this, and you should. Along with this prep, you’ll need to be proactive and forward-thinking. It’s impossible to mitigate every risk, as we learn in the report, Ransomware Through the Lens of Threat & Vulnerability Management.
Next, we’ll review some of the report’s biggest findings.
Breaking Down the Ransomware Report
This study has some great data in it that you and your team can learn from. Here’s my take on the findings:
Ransomware Vulnerabilities Increase
The report lists a 19% increase in vulnerabilities associated with ransomware, bringing the total in 2022 to 344. Researchers also mapped these to MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK). In doing so, they found 57 highly dangerous out of 81 unique end-to-end products. The most common were Microsoft, Oracle, VMWare, Atlassian, Apache, and SonicWall.
Scanning Tools Aren’t Catching These Vulnerabilities
You likely depend on scanning tools, like Nessus, Nexpose, or Qualys, but they aren’t detecting some of the serious issues. A total of 20 vulnerabilities were not detectable with these popular scanners, and all of these were old and discovered between 2010 and 2019. It’s not too abnormal for this, as cybercriminals are always reinventing their attack strategies. They are constantly refining and seeking to get past your defenses.
Trending: New CWEs
The report found that 80 CWEs (Common Weakness Enumerations) are contributing vulnerabilities that ransomware can exploit. This is a 54% increase over 2021. The problem — it seems, is that companies are releasing software and applications without a thorough evaluation of the code. Such a statistic highlights the race to get a product to market and extend releases. It would seem that DevSecOps adoption may be faltering.
Whether you’re a cyber professional or a regular software user, there’s an expectation that the application will be secure by design. It points to a larger conversation about why security and development aren’t tighter. Security and innovation can play well together; they are not foes. To me, you can’t deliver the best software experience without weaving security throughout its design.
Ransomware Attackers Are Highly Sophisticated
Many of the groups launching ransomware attacks aren’t your everyday hackers. They belong to APT (Advanced Persistent Threat) groups. Many have connections to nation-states and seek to cause havoc to infrastructure. So, it’s not all about the potential for money. The report highlights the rise of ransomware before the actual war between Russia and Ukraine. Russian hacking groups targeted critical infrastructure in Ukraine.
Researchers also named China and North Korea as countries with APTs, and they believe this trend will only rise. Cyberwar is the newest playing field for conflict.
Old Vulnerabilities, New Attacks
As noted in the opening, 76% of ransomware-associated vulnerabilities date back to pre-2020. There is cause for concern when digging into this a bit more. The report calls out 264 old vulnerabilities, and 208 have publicly available exploits. The most significant data point from this section is that 119 of these are actively trending on the dark web as of interest to hackers.
Next, the analysts examined which products had these old vulnerabilities, with Windows 11, Enterprise Linux, openSUSE, and Linux having the most. Recall also that 20 of these were not detectable by the best scanners.
All of this points to the issue of cyber hygiene. It’s a good time to examine how you maintain system health and improve security. Much of this can be associated with the same-old challenges of legacy systems, unpatched components, and “shadow” IT assets. They are the favorite entryways for hackers, and as long as we, the good guys, don’t address them, they have an easy way to get inside and do damage.
Putting a spotlight on this will beget greater visibility, but this may be a deeper problem that has a lot to do with your people. I don’t mean your technical folks aren’t good at cybersecurity. They likely are. What they often aren’t good at is communication, adaptability, flexibility, and uncertainty. However, these are attributes of the job. When they don’t evolve their mindset, security vulnerabilities will persist. They prefer the status quo and certainly don’t want anyone challenging them. That’s when they get defensive, and that’s not the type of defense you want them playing.
It’s a problem that encircles some other trends.
More Ransomware Trends and Predictions
The report also offers some insights on what to expect. In 2022, phishing, email compromise, stolen credentials, and vulnerabilities enabled ransomware attacks. These have been standard entryways, so the focus goes back to what’s happening with vulnerability management.
The foundations of a good program are processes, people, and technology. Technology can assist, but you need robust protocols and people that will think critically and act, which requires them to move outside their comfort zone. So, yes, this is a people problem, too.
Another trend I’ve written about is the proliferation of AI. It’s become very accessible, which has pros and cons. Bad guys will use it the same way the good guys are.
So, what does all this mean in the picture of how your people will evolve and be better at combatting ransomware?
So, there are a lot of people gaps in protecting against ransomware. It’s not something you can’t change. I developed a system to do just that with the Secure Methodology™. It’s a seven-step guide to help cyber leaders transform staff into highly communicative, collaborative, and adaptable professionals.
The Future of Ransomware Defense: People Matter
Your cyber team won’t magically change overnight and develop the people skills they need to win the cyber war. It’s a process, which is why there are seven steps. Each of these connects to how technical people act and feel. The problem is that they have little awareness of how these actions and feelings heighten risk and deter collaboration. You have the opportunity to open their minds to this and connect it to being a better cyber professional (and, possibly, person!).
If you present this to them as something that’s not threatening, they’ll be more receptive. It’s still change, which is hard for anyone in any situation. Remember, these people don’t like to be wrong. They want to be the smartest person in the room. So, they’ll resist when they hear they aren’t and need to adapt. But that’s the point of becoming better at work or in life.
Here are the main things that the Secure Methodology can do for you and your team.
- It can teach them real skills on how to communicate, which includes listening and understanding nonverbal cues. They’ll have to leave behind their geek speak and adopt a more inclusive language. There are exercises in the Secure Methodology to facilitate this.
- It can expand their mindset. People can’t grow when they have a closed mindset. Opening up will help them reframe their perspective, which can create some “aha” moments.
- It can help them be more empathetic. Empathy is an essential trait for technical people. If they can understand the position of others, even hackers, they’ll be better prepared to defend against them. Empathy within the team also cultivates trust and respect.
Ransomware will continue to be a considerable threat to any organization. The numbers tell the story, and you have to be creative in how to thwart it. Your people are the most crucial component, and the more you can develop their non-technical skills, the better.
You can learn more about the Secure Methodology by reading my book, The Smartest Person in the Room, and checking out the course, now available.
 In the field of cybersecurity, there are always opportunities to learn. It’s a dynamic ecosystem that’s always changing in terms of threats. There’s also no shortage of cybersecurity breaches, with fear-inducing headlines that can make any company shutter. But I’d also argue there is much to learn in these situations.
In the field of cybersecurity, there are always opportunities to learn. It’s a dynamic ecosystem that’s always changing in terms of threats. There’s also no shortage of cybersecurity breaches, with fear-inducing headlines that can make any company shutter. But I’d also argue there is much to learn in these situations.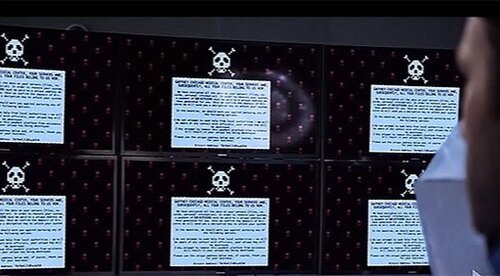 Last night I watched an episode of
Last night I watched an episode of 



